PCI DSS 4.0 requirements are no longer a future project. On March 31, 2025, the future-dated requirements became effective. The PCI Security Standards Council (PCI SSC) made it explicit in the v4.0.1 specifications and guidance.
Now, some merchants may mention that the deadline is in 2026. This is because the updated SAQs for PCI DSS v4.0.1 were published in October 2024, and the v4.0.1 ROC template was published in August 2024. Therefore, 2026 will be the year when the argument “we are still catching up” falls short for most merchants and service providers.
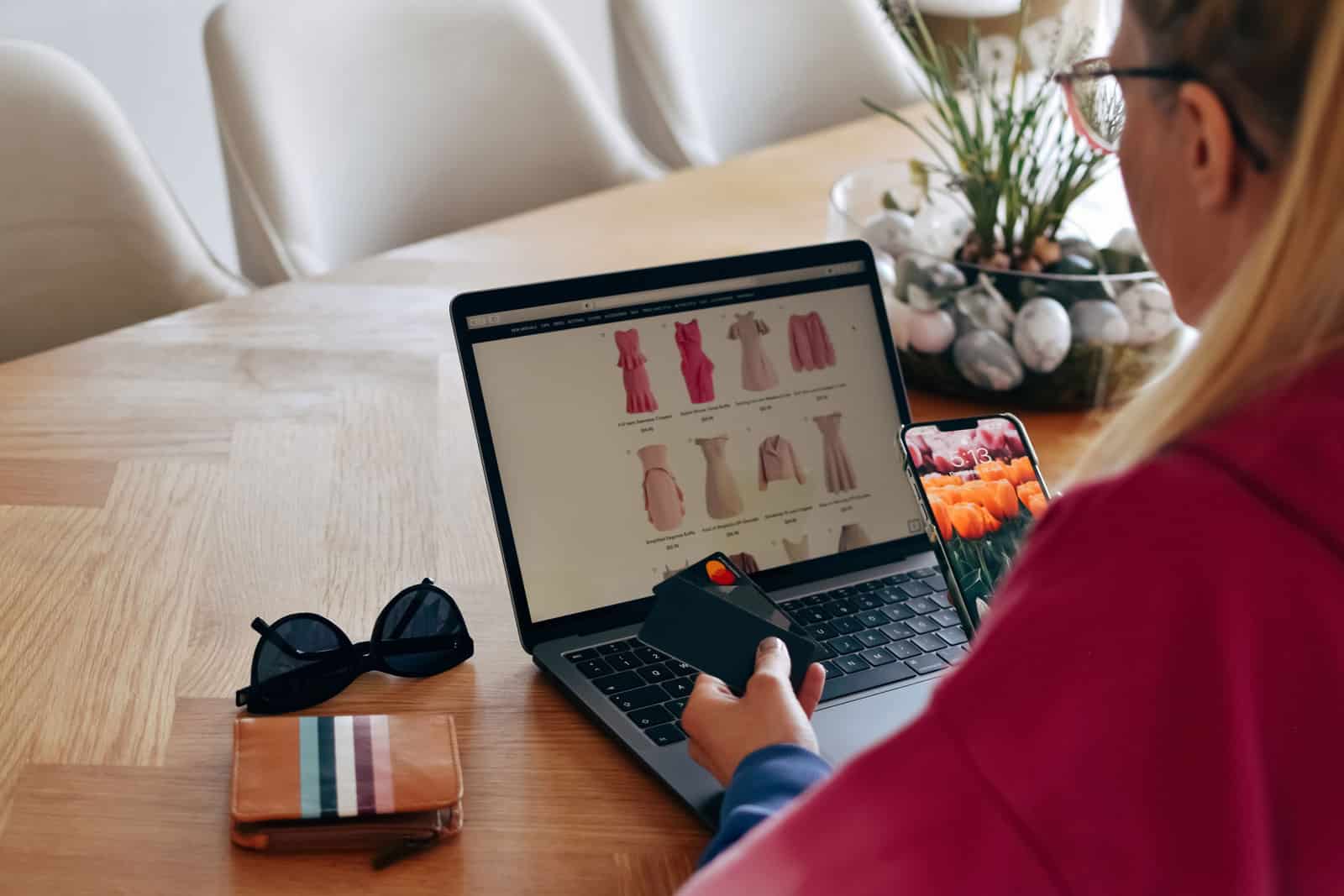
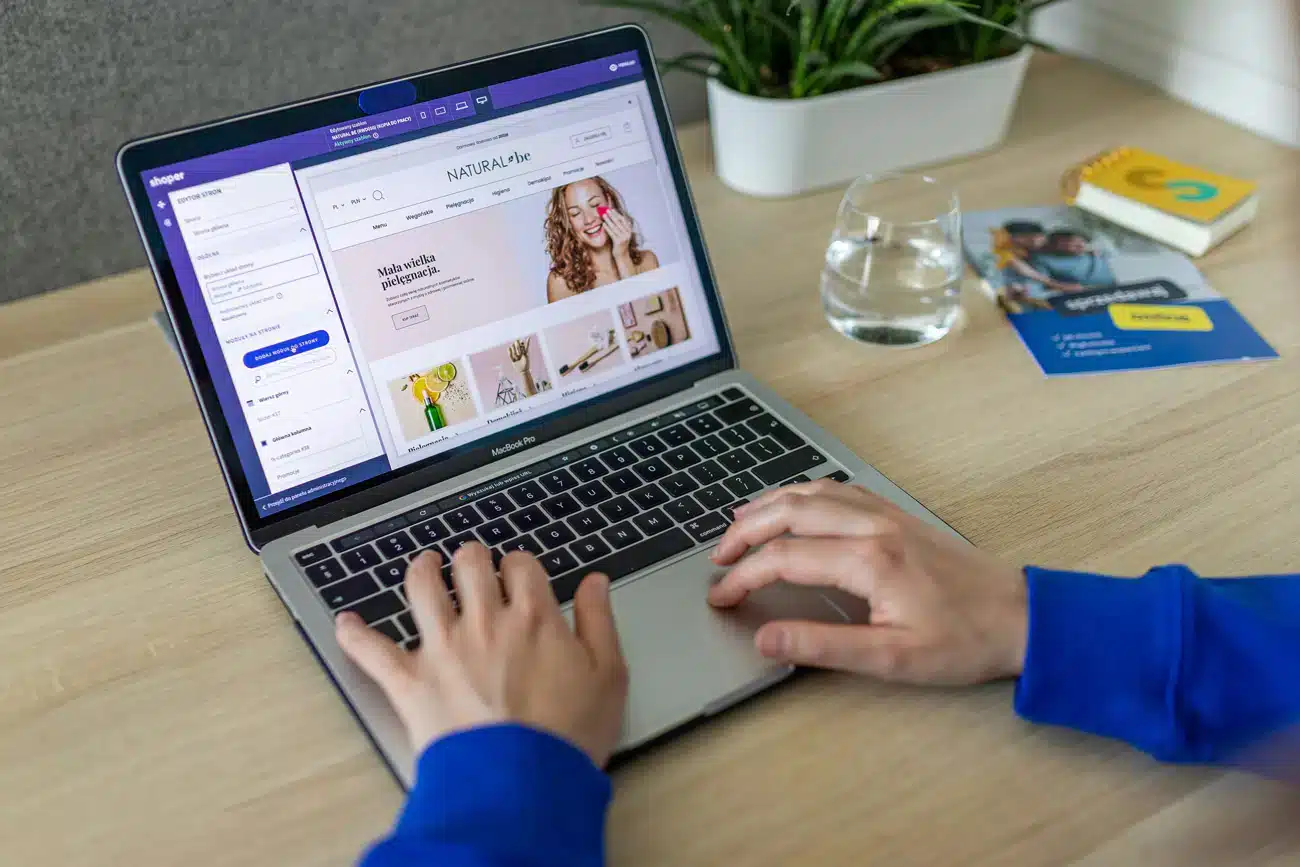
This is especially true for e-commerce merchants. The new version of PCI DSS v4.x places merchants under a stricter requirement to secure their payment pages. It also mandates the use of more comprehensive authentication and documentation.
This article will explain the changes that were made to the new PCI DSS 4.0, what PCI DSS 4.0 requirements merchants need to be aware of in 2026, the changes made to PCI DSS 4.0 authentication requirements, and what merchants should do now in response to treating the PCI DSS 4.0 deadline and March 2025 requirements as a future problem.
What PCI DSS 4.0 Actually Changed
The latest version of the standard, v4.0, marks the first major update in over a decade. The update introduced 64 new requirements, 51 of which are scheduled to become active on March 31, 2025. PCI DSS v4.0.1, published in June 2024, did not introduce any new requirements or remove any existing ones. Instead, the specification clarified the wording of certain requirements and left March 31, 2025, as the effective date.
The fact that there were no new requirements means there were changes to how the standard operates. For instance, the standard requires that entities perform a risk analysis to determine the frequency with which certain requirements must be met. Additionally, there are new controls regarding script execution on the payment pages, authentication, and the length of passwords required to access public web applications. While these may not seem like significant changes at first, they are infrastructural changes.
The PCI DSS 4.0 Authentication Requirements That Matter Most
The following are authentication requirements within the new PCI DSS 4.0 standard. These are another area in which many merchants underestimate the effort that is required. Requirement 8.4.2 in SAQ D for merchants states that multi-factor authentication must be implemented for all access to the cardholder data environment. Requirement 8.3.6 also indicates that passwords or passphrases must be at least 12 characters long, or at least 8 characters if the system does not support 12-character passwords. This requirement took effect on March 31, 2025.
This is a significant change and will impact how merchants manage access to the CDE. This is especially true if a merchant has many legacy processes and access methods for administrators.
The FAQs published by the PCI Security Standards Council in 2025 and 2026 provide further details on these requirements. In May 2025, the PCI SSC said that using phishing-resistant authentication alone is not sufficient to satisfy requirements 8.4.1 or 8.4.3. It must be used in conjunction with another authentication factor. However, in a separate FAQ also published in May 2025, the PCI Security Standards Council said that using synced passkeys, as defined in FIDO2, could be used as the single factor for phishing-resistant authentication and replace the need for multi-factor authentication under requirement 8.4.2.
This example shows how the PCI DSS 4.0 standard will apply to merchants. The standard does not simply state that multi-factor authentication is required. Rather, it requires that merchants understand which users, systems, and access are required, and the method of authentication to be used.
What Merchants Should Do Before 2026 Assessment Cycles
The first thing merchants should do is re-scope their environment based on the updated information from PCI SSC. If a merchant chooses to use a redirect or custom payment pages, they could end up in a different compliance scenario.
The second thing merchants should do is to fully inventory the different elements that may affect the payment page. This includes scripts that run in the browser, content delivery networks, payment systems, and third-party tools.
The third thing merchants should do is review their identity and access controls against the new standard. This includes reviewing password length, multi-factor authentication, administrative access, and access to service accounts for legacy systems.
The fourth thing merchants should do is to review and create proper documentation. The introduction of a risk analysis requirement for specific PCI DSS v4.0 requirements prompted guidance from the PCI SSC. If a merchant sets the frequency for certain periodic activities, they must have proper documentation to justify this decision.
What’s Getting Harder and What’s Getting Easier
What is getting harder is informal compliance. The ability of merchants to rely on scripts and components that simply “work” for them, and the lack of formal reviews each year of what merchants are doing with their PCI DSS 4.0 compliance, is limiting.
What is getting easier is clarity. The PCI SSC spent the last two years putting out information about the transition, the new SAQs, the new FAQs, and the specific clarifications they have made for e-commerce merchants. While this does not reduce the amount of work required, it makes it easier for merchants to comply in the operational context.
The PCI DSS 4.0 Requirements Merchants Are Still Catching Up To
Payment-page security is now a core merchant issue
One of the biggest changes to the PCI DSS 4.0 requirements is that PCI SSC focuses on the security of the payment page within the browser. Requirement 6.4.3, which is about the management of scripts that are loaded and executed on the payment page within the consumer’s browser, is a new requirement that was made required after March 31, 2025. This guidance, included in the discussion of payment page security and e-skimming, requires that merchants ensure that any scripts loaded on a payment page are authorized, have had their integrity ensured, and that changes to that script are detected. For many merchants, this is a significant change. The use of scripts on payment pages is widespread, and merchants have to ensure that all scripts are authorized, the integrity of the scripts is maintained, and that any changes to those scripts are detected.
Public-facing web application protection got stricter
Requirement 6.4.2, which requires that a merchant deploy an automated technical solution to detect and prevent web attacks on public-facing web applications, is a new requirement that was introduced and that replaced the periodic review of those web applications. The materials for both SAQ and SAQ A-EP indicate that this requirement became effective on April 3, 2025. This means that merchants can no longer solely rely on the annual penetration test to provide adequate security for their public-facing web applications.
FAQs
Q: What is PCI DSS 4.0?
A: The current version of the standard, PCI DSS 4.0, was released by the PCI Security Standards Council (PCI SSC). According to the PCI SSC, there are 64 new requirements in this version, 51 of which are future-dated to March 31, 2025. After this date, these requirements will be fully effective in the assessment requirements.
This version of the standard focuses on enhancing the requirements for merchants regarding browser-side security in the payment transaction.
Q: What are the PCI DSS 4.0 authentication requirements merchants should focus on first?
A: The PCI DSS 4.0 authentication requirements that most merchants should focus on are the new requirements for multifactor authentication and passwords. The SAQ D for merchants indicates that Requirement 8.4.2 requires multifactor authentication for access to the cardholder data environment. Furthermore, Requirement 8.3.6 requires that the password or passphrase be at least 12 characters long, unless the system supports only 8 characters.
The latter FAQs from the PCI SSC also indicate that using phishing-resistant authentication is not enough to satisfy Requirement 8.4.1 and 8.4.3, but using FIDO2 passkeys would satisfy Requirement 8.4.2.
Q: What happened to the PCI DSS 4.0 deadline, March 2025 requirements?
A: The deadline for March 2025 for PCI DSS 4.0 is not the deadline for 2026. The future-dated requirements are effective on March 31, 2025. The v4.0.1 release of the standard did not modify this to a 2026 date.
When people refer to the 2026 deadline, they are referring to the first assessment, the filing of the SAQ, the ROC, or the acquirer remediation. These dates will be when the 2025 requirements become fully effective for merchants.
Q: Do SAQ A merchants still need to worry about payment-page security under PCI DSS 4.0?
A: Yes. The PCI SSC has moved the removal of the requirements for Requirement 6.4.3 and 11.6.1 from the SAQ A category to a new eligibility criterion. However, the PCI SSC also clarified that these changes do not remove or diminish the requirements of PCI DSS. If a merchant is using embedded payment pages, the PCI SSC requires that the site not be susceptible to script attacks that could impact the e-commerce site and system.
Conclusion
The real story behind PCI DSS 4.0 in 2026 will not be that there was a sudden new deadline. Instead, 2025 is behind us, and merchants that delayed implementing this standard are facing the consequences of being assessed under the v4.0.1 standard.
Merchants should focus on four different areas. If these four areas are up to date, managing PCI DSS 4.0 will be much easier for merchants. If these areas are not up to date, 2026 will be the year in which this becomes difficult to ignore.
Sources
- PCI Security Standards Council. “Just Published: PCI DSS v4.0.1.” Accessed March 2026.
- PCI Security Standards Council. “Now Is the Time for Organizations to Adopt the Future-Dated Requirements of PCI DSS v4.x.” Accessed March 2026.
- PCI Security Standards Council. “SAQs for PCI DSS v4.0.1 Now Available.” Accessed March 2026.
- PCI Security Standards Council. “PCI SSC Releases ROC Template for PCI DSS v4.0.1.” Accessed March 2026.
- PCI Security Standards Council. “PCI DSS Summary of Changes From Version 3.2.1 to 4.0.” Accessed March 2026.
- PCI Security Standards Council. “Important Updates Announced for Merchants Validating to Self-Assessment Questionnaire A.” Accessed March 2026.
- PCI Security Standards Council. “FAQ Clarifies New SAQ A Eligibility Criteria for E-Commerce Merchants.” Accessed March 2026.
- PCI Security Standards Council. “Guidance for PCI DSS Requirements 6.4.3 and 11.6.1: Payment Page Security and Preventing E-Skimming.” Accessed March 2026.
- PCI Security Standards Council. “Just Published: PCI DSS v4.x Targeted Risk Analysis Guidance.” Accessed March 2026.
- PCI Security Standards Council. “Is Phishing-Resistant Authentication Alone Acceptable as Multi-Factor Authentication for PCI DSS Requirements 8.4.1 and 8.4.3?” Accessed March 2026.
- PCI Security Standards Council. “Are Passkeys Synced Across Devices, Implemented According to the FIDO2 Requirements, Acceptable for Use as Phishing-Resistant Authentication to Meet PCI DSS Requirement 8.4.2?” Accessed March 2026.
- PCI Security Standards Council. “PCI DSS v4.0 SAQ D for Merchants.” Accessed March 2026.